
Leading in times of crisis: How healthy optimism works
Crises are as much a part of business as stormy weather at sea. But what if the storm lasts longer? 3 impulses for strong leadership in a crisis.

The pandemic poses enough problems – cyber-attacks shouldn’t be one of them. How can companies protect their systems thoroughly and prepare themselves against new threats?
Cyber-attacks on companies and public institutions have become so commonplace that they hardly cause any sensation. Recently however, this was different: In the midst of the pandemic, criminals attacked healthcare systems. Industrial spies allegedly captured sensitive data on a new Covid-19 vaccine from servers of the European Medicines Agency. Hospitals were targeted, e.g. the University Hospital in Düsseldorf, Germany. It’s clear that such cases cause much greater anxiety than cybercrimes which affect other societal spheres.
However, the problem affects all sectors, and the consequences can be significant. The most recent spectacular case: a possible data theft from a file-sharing platform of the New Zealand Central Bank. The fact that well-known institutions are caught off guard by hackers may surprise non-professionals, but not IT security experts – especially in the current crisis. There are two sides to the problem: Right now other issues may seem more urgent than cyber security. At the same time, new targets for attacks are emerging, e.g. fostered by the trend toward working from home and quickly provided remote access.
Now, at the beginning of the second year of the Covid-19 crisis, it is recommended to perform a checkup of the IT immune system. The following key areas are relevant:
Everyday behaviour
Currently, an above-average number of employees are accessing company systems from home. This makes conscientious behavior particularly important. For instance, the company’s VPN access may be secure but the connection to the private printer or other devices in the home network is not. It might therefore be a good idea to start an awareness campaign about security risks.
Regulated outsourcing
Companies need clear quality criteria and security rules for all IT areas that rely on external service providers, e.g. a cloud framework and so-called whitelists: Which data must be encrypted? Who is allowed to use our systems and documents, and in which way? Which cloud services can employees access?
Detecting and managing incidents
In order to identify data leaks or cyber-attacks at an early stage, companies can set up a Security Operation Center (SOC). The SOC monitors all systems and triggers an alarm in case of anomalies, e.g. if large amounts of data are being downloaded at an unusual time. The organization must be well prepared for such an emergency. For example, data backups should be up-to-date, and a redundant e-mail system should be available.
Protecting critical systems
Depending on the industry, different IT services are indispensable for day-to-day business. Companies should take the maximum security measures, both technically and organizationally: with strictly limited access rights, comprehensive backups, regular penetration tests and a central monitoring unit.
Shielding sensitive data
Typical gateways for hackers can be blocked technically, for example by encrypting e-mails and drives. It’s also advisable to have a user concept that classifies systems and data and defines exactly who is allowed to access them.
Extra protection for productivity
IT must be protected not only virtually, but also physically. Companies should house their critical infrastructure in a way that it can resist fires, earthquakes or floods. At best, the company should have a backup system at another location.
The aspects described here are only an excerpt from a comprehensive concept that we apply in our work for our customers: Our “House of IT Security”defines all the criteria we use to assess a company’s IT defenses. Starting from this analysis, important next steps can be derived to make the systems more secure – even and especially in times of crisis, and without overburdening the organization.

Crises are as much a part of business as stormy weather at sea. But what if the storm lasts longer? 3 impulses for strong leadership in a crisis.
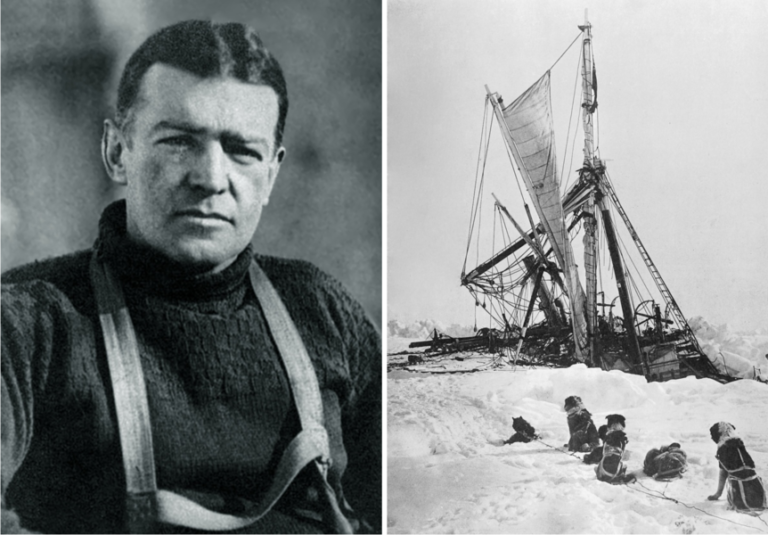
He conveyed confidence in a desperate situation: British polar explorer Ernest Shackleton and his team survived a two-year battle for survival in the Southern Ocean. What can leaders learn from him in times of crisis?
Getting an IT project across hundreds of organizational units to the finish line? Our colleague Mathis takes a sporty approach. In our interview, he tells us what excites him about project management as a consultant and why he goes to the boxing ring to compensate.
2021 Grosse-Hornke Private Consult